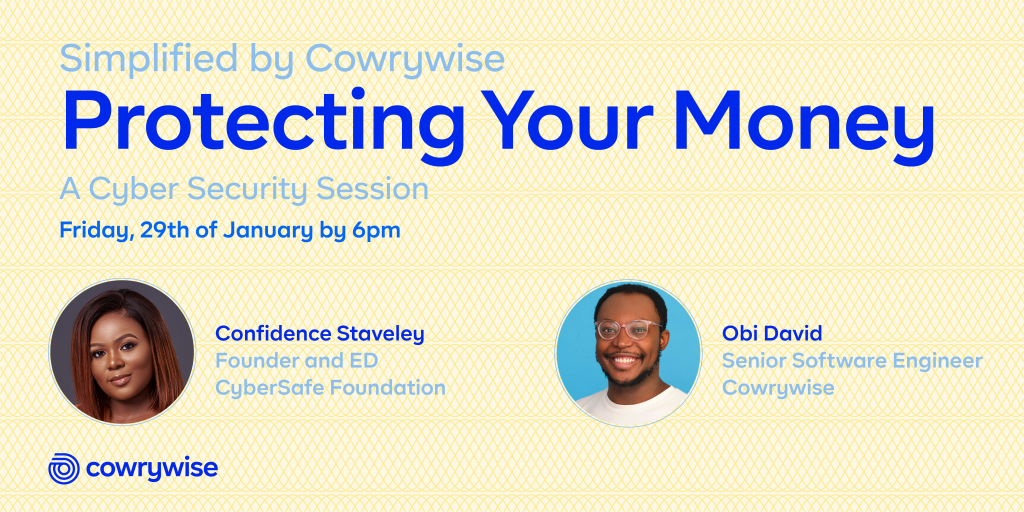
We now live in a “cashless society” that prioritizes sending and receiving money online, instead of carrying notes around. This ‘Simplified by Cowrywise’ session on Cyber Security, therefore, focused on helping you protect your money from internet fraudsters who device new tactics as you become more aware of their old ones.
Simplified by Cowrywise are events periodically held to help break down how money works for everyday people. Confidence Staveley, the Founder and Ed of CyberSafe Foundation and Obi David, a Senior Software Engineer at Cowrywise shared interesting points at this Simplified event on protecting your money. Here’s a summary from their sessions.
Cyber Security Tips From Confidence Staveley
When you think about protecting your money, what comes to mind?
- Putting a padlock on your safe?
- Protecting the vault room?
You’re on the right track if these answers are similar to what you’re thinking but your thoughts should go beyond the traditional bank setting. As long as you’re consuming services online, you have a role to play in security.
The CyberSafe Foundation team organized a vox pop around Yaba, Lagos and 70% of the people who participated shared their ATM pins and Social Media passwords. They shared such sensitive information with the hopes of winning a fake freebie the CyberSafe Foundation team had promised them. And this included young people. ?
Rather than being the exception, this is sadly the norm. A potent way cybercriminals now use to get young (and old) people to share sensitive information is called Social Engineering. This is the art of manipulating people to disclose confidential information, by impersonating trusted people and organizations.
Many cyber frauds are successful because they realize that it is now easier to hack humans than it is to hack computers. That’s why they use Social Engineering.
Why Do Cybercriminals Do What They Do?
Although they can work for different reasons, their top motivation is to have access to your money. Financially motivated crimes are big around here and your money is attractive.
That’s why gaining the relevant knowledge to stay ahead of their tactics is an investment everyone should take seriously. Knowing what the opponent is doing is one of the best ways to secure yourself.
Red Flags To Watch Out For
Investment scams with unrealistic ROI (Return on Investment) – These scams have become big because people are looking for ways to multiply their money. However, if it looks too good to be true then it most likely is bad for you.
Phishing – Social engineering that happen over emails and text messages. They are circulated in different forms, especially with links so you must find ways to detect them.
5 Tips to Identify Harmful Links
- Treat every link as suspicious. Avoid clicking links in emails, social media and text messages. Instead, manually type them out in your browser
- Hover your cursor over the link. When using your phone, press and hold down the link to see where it intends to lead you
- Watch out for lookalike domains. One glance is not enough as Netflix and Netfiix are not the same, just as ncdc.gov.ng and ncdc.com.ng are not the same
- Inspect shortened links with popular sites like www.checkshorturl.com
- Use a link scanner. They are websites and plugins that allow you to detect suspicious web addresses, for example, www.virustotal.com as recommended by Confidence
How to Protect Yourself
- Do not share sensitive information like OTPs, BVN, Debit/Credit Card details + passwords openly
- Put on 2FA (extra bodyguards) on all platforms
- Do not use your date of birth as your pin or password
- Use strong passwords that contain upper and lowercase letters, as well as numbers and special characters that do not contain easy to guess information like your name or date of birth
- Use a good password manager, which is like a vault to securely store your passwords
- Be click wary and mindful of clicking on links that lead to freebies
Data Privacy and Cyber Security by Obi David
Many people think of hackers as people wearing black hoodies with a dark or scary face, but hackers look like normal human beings – like everyday people.
Cyber Security is Important but Privacy is an Illusion
Some of the most secure platforms have been involved in data breaches and it continues to be a source of major concern. But data does not breach itself, people do and it may be for one or more of these reasons:
- To make money from it
- To gain employment in some cases (some organizations that have been hacked end up employing the hacker to work for or with them)
- For political motives to push ads and other information to people
- For fun
Are You Vulnerable?
Yes – if you have anything that connects you to the internet
How To Protect Yourself
- Use strong and different passwords so that if one of your accounts is compromised, they wouldn’t be able to guess correctly the passwords to other platforms
- Do not connect to public wifi networks
- Don’t post your sensitive details online
- Enable 2FA on all platforms
- Do not use the same passwords you use on sensitive apps on places you solicit for freebies
- Do not share your bank OTP
- Avoid free anti-virus software
- Do not store your passwords in plain text in your email, phone notepad, etc
- Do not store your debit card details on your browsers – use applications like LastPass/ One Password instead
- Don’t be a greedy person who falls for obvious scams or money doubling promises
How Cowrywise Keeps Your Money Safe
- We’ve partnered with Paystack to provide the highest level of security. Paystack is PCI DSS Level 1 Certified
- Token 2FA. See this as the extra bodyguard you have on your account
- We verify your Identity through your BVN (Your name, date of birth and phone number are the only information we have access to)
- Cyber Security is important to us so we operate a fraud detection system. This system watches for fraudulent activities and flags such accounts
- With a 256-Bit SSL encryption. This means that all transactions are encrypted and cannot be accessed by a middle man
What You Should Not Do
- Do not ignore these points because you believe you’re too smart to be hacked
- Do not leave the internet to stay “safe”. Instead, let the internet work in your favour
To download David’s slide on Data Privacy and Security, click here.
What lessons are you going to take more seriously from now?
Share with us in the comments below. Remember to also send this to your friends and family.
To watch the full session, please click the link below and subscribe!
